Traffic von 23.225.141.70 – Oder: Von SYN-Floods und schwarzen Löchern
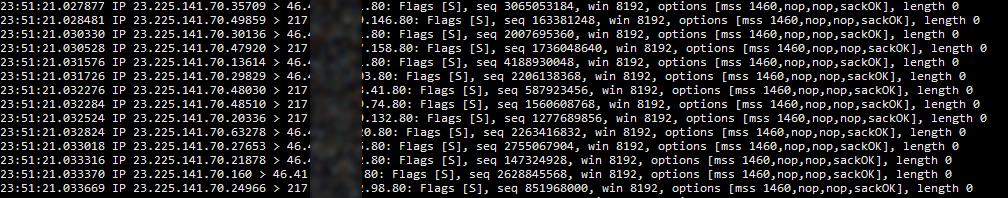
Gestern (26. September 2018) wurde ich gewahr, dass da ziemlich eigenartiger Traffic von der IP-Adresse 23.225.141.70 auf nahezu alle meine Server einschlägt.
Da handelte es sich um (vergleichsweise) große Mengen an TCP-SYN-Paketen, gerichtet an Port 80 auf meinen Systemen.
Gemäß dem Enten-Test schlussfolgerte ich:
- Es sieht aus wie ein SYN-Flood
- Es fühlt sich an wie ein SYN-Flood
- Es hat tendenziell Auswirkungen wie ein SYN-Flood
- Es muss also ein SYN-Flood sein!
Elendige Schweinepriester! Warum attackieren die mein System! Aber vorsicht: Ganz so einfach ist es dann doch nicht!
Wenn es kein SYN-Flood ist, was ist es dann?
Spoiler-Alarm: Es ist kein SYN-Flood! Tatsächlich ist das eine hinterhältige DDoS-Attacke gegen die IP-Adresse 23.225.141.70.
Die Idee dahinter ist:
Der TCP-Handshake arbeitet so, dass man ein SYN-Paket zum Server schickt um eine Verbindung zu öffnen.
Dieser antwortet mit darauf mit SYN-ACK und der Client dann wieder mit ACK - und dann hat man seine TCP-Verbindung und kann Daten übertragen.
Erfolgt allerdings keine Antwort auf das SYN-ACK des Servers wird dieses Paket (wie das bei TCP halt nunmal so ist) mehrfach erneut gesendet.
Schickt nun jemand mit gespoofeter IP-Adresse (nämlich mit der des DDoS-Opfers) ein SYN-Paket an einen offenen Port eines beliebigen Servers im Internet,
wird dieser Server also wie erwartet SYN-ACK schicken. Und weil keine Antwort kommt, direkt noch einmal. Und nochmal...
Das wiederholt sich insgesamt (abhängig vom Betriebssystem und dessen Konfiguration) im Durchschnitt 3-5 Mal bis der Server aufgibt.
Oder anders gesagt: Schicke ich an 100.000 Server im Internet ein SYN-Paket wird das Opfer ca. 500.000 SYN-ACK-Pakete erhalten.
So kann eine enorm hohe Paketrate erreicht werden, die das Opfer irgendwann aus dem Internet wirft.
Wenn die Paketrate hoch genug ist (im Bereich von einigen zehn bis hundert Millionen Paketen pro Sekunde) kann damit auch das Routing-Equipment vollkommen überlastet werden,
womit dann neben dem eigentlich attackierten Opfer auch das restliche Netzwerk drumherum gestört wird.
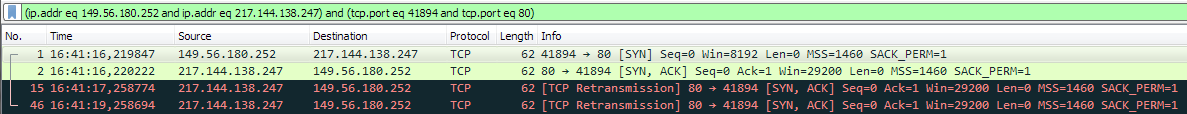 Das ist ein Screenshot aus Wireshark. Er zeigt ein anderes Event eines SYN-ACK-Floods (daher auch die andere IP-Adresse). Hier sieht man ein eingehendes SYN-Paket von IP 149.56.180.252 kommen - und die drei Antworten, die mein Server schickt, bevor er aufgibt.
Das ist ein Screenshot aus Wireshark. Er zeigt ein anderes Event eines SYN-ACK-Floods (daher auch die andere IP-Adresse). Hier sieht man ein eingehendes SYN-Paket von IP 149.56.180.252 kommen - und die drei Antworten, die mein Server schickt, bevor er aufgibt.
Im gesamten Internet finden sich für diesen Zweck auch genügend Server mit genügend offenen TCP-Ports, die sich dafür missbrauchen lassen.
Auf einem der Core-Router habe ich mal live Traffic von dieser IP-Adresse gespiegelt – und war insgesamt doch echt beeindruckt:
Locker mehrere Hundert Anfragen pro Sekunde an hunderte verschieden IP-Adressen! Alleine in unserem Netz dürften so auf diese Weise gut 1.000 SYN-ACK-Pakete pro Sekunde entstanden sein.
Das schwarze Loch
Diese zahlreich generierten SYN-ACKs der angesprochenen Server kamen allerdings zu dem Zeitpunkt als ich das tiefer prüfte schon gar nicht mehr beim Opfer an –
denn die attackierte IP-Adresse war bereits in ein Blackholing aufgenommen worden:
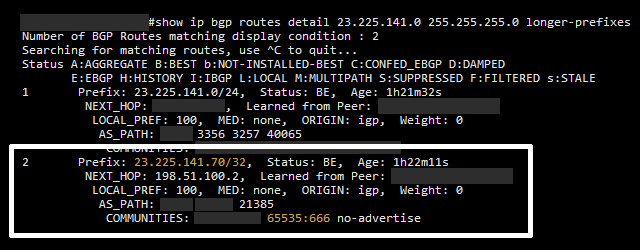
Dazu wird eine BGP-Route für die attackierte IPv4-Adresse erstellt (weißer Kasten), mit der quasi-genormten BGP-Community 65535:666 versehen (ganz unten orange markiert) und in die Welt geschickt.
Die Routen mit dieser speziellen Community werden i.d.R. überall speziell verarbeitet und als Nullroute in die Router der Provider und Carrier eingefügt – so auch bei uns.
Der Effekt ist dann, dass der DDoS-Traffic zu dieser IP-Adresse (den man ja definitiv nicht haben will) so früh wie möglich gestoppt wird und nirgendwo Netze verstopft.
Natürlich bekommt das Ziel so auch keinen legitimen Traffic mehr und ist (das ist ja das Ziel einer solchen Attacke) erstmal offline.
Allerdings ist dann nur diese eine attackierte IP nicht erreichbar, nicht im Zweifel das gesamte restliche Netzwerk.
Die SYN-ACK-Pakete in Richtung dieser IP-Adresse sind also weisungsgemäß vom Router verworfen worden und sozusagen in einem schwarzen Loch verschwunden.
Allerdings kamen weiterhin diese gespoofeten SYN-Pakete herein und haben auch erstmal dazu geführt, dass Systeme ins Logfile geschrieben haben, dass sie einen SYN-Flood von dieser IP detektiert hätten.
Jedoch: In der ganzen Geschichte ist diese IP-Adresse das Opfer und die Betreiber des betroffenen Systems hatten sicherlich auch ein großes Interesse daran, dass das irgendwann wieder aufhört ;-)
Also kein SYN-Flood sondern ein ziemlich zünftiger DDoS, gegen den man sich tatsächlich nur schwer mit herkömmlichen Mitteln schützen kann.